I’ve written about two unethical situations: Gift Card Churning – Is This Another Scummy Move? and most recently Unethical, Profitable Gift Card Churning Machine. Both eliciting a good and bad response that I appreciate to see all the views that I might have missed.
Before we delve into the why’s let’s review a white hat and black hat from Wikipedia:
White hat
Main article: White hatA white hat hacker breaks security for non-malicious reasons, perhaps to test their own security system or while working for a security company which makes security software. The term “white hat” in Internet slang refers to an ethical hacker. This classification also includes individuals who perform penetration tests and vulnerability assessments within a contractual agreement. The EC-Council,[8] also known as the International Council of Electronic Commerce Consultants, is one of those organizations that have developed certifications, courseware, classes, and online training covering the diverse arena of Ethical Hacking.[7]
Black hat
A “black hat” hacker is a hacker who “violates computer security for little reason beyond maliciousness or for personal gain” (Moore, 2005).[9] Black hat hackers form the stereotypical, illegal hacking groups often portrayed in popular culture, and are “the epitome of all that the public fears in a computer criminal”.[10] Black hat hackers break into secure networks to destroy data or make the network unusable for those who are authorized to use the network. Black hat hackers also are referred to as the “crackers” within the security industry and by modern programmers. Crackers keep the awareness of the vulnerabilities to themselves and do not notify the general public or manufacturer for patches to be applied. Individual freedom and accessibility is promoted over privacy and security. Once they have gained control over a system, they may apply patches or fixes to the system only to keep their reigning control. Richard Stallman invented the definition to express the maliciousness of a criminal hacker versus a white hat hacker who performs hacking duties to identify places to repair.[11]
Now that you understand the differences, when you’ve manufactured spend enough, you will engage in areas where the lines blur or are clearly defined. The two posts above are clearly defined that the lines have been crossed of being acceptable and ethical. For the record, I’ve done each once to confirm the findings. I’d like to think that I engage in the white hat aspects of manufactured spending, but some would think manufacture spending already is already crossing the line.
When you find a vulnerability like this, for outsiders like ourselves, who do we tell when you find out? Thankfully, the Internet has connected us in ways we wouldn’t have thought of years ago. For the Unethical, Profitable Gift Card Churning Machine post, I’ve searched LinkedIn, but I couldn’t pinpoint anyone in the company that I could send to notify. An additional wrinkle is that it’s a subsidiary of a larger company.
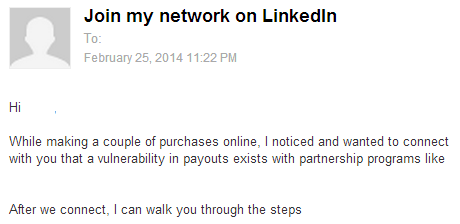
For Gift Card Churning – Is This Another Scummy Move?, it was pretty easy to find the SVP of Ecommerce on LinkedIn and I let him know of the vulnerability. Because I am not a premium member on LinkedIn and this person is not any where near my relationship circles, I had to leave him a short message that I’ve redacted a bit.
It could be coincidental or it could have been the message I sent to the SVP, who knows because he never responded. But after seeing what happens with the impact to everyone using the portal, I will refrain from researching and playing around with vendors and portals when I spot something that I feel obligated to need to tell someone at the company. I don’t want to be chased with pitchforks with people looking for blood at a public setting because I “killed” their deal.
> For the Unethical, Profitable Gift Card Churning Machine post
The company knows abouts the workaround you eluded to in that post.
My biggest concern with MS is the credit card fraud aspect.
Did they? I’m glad they were able to square it away
You’ve aroused my interest. Please send the password. Thanks.
I can imagine some of these technique require amount of works and times to accomplish. I don’t think it will work for anybody. The Golden Era of MS has already been gone.
It’s true, it takes a lot of time, if you constantly repeat the process having a test script makes the process a little easier like having a check list of things to do
I’m curious why you felt you needed to play police on this one while you still engage in practices that others would consider unethical. The very practice of cc churning is not allowed per their terms of service. Read any credit card agreement and you will find that psuedo spending (read gc churning, free cash advances, etc) are not allowed when it comes to earning points. Yet you do it. Are you going to call Amex and tell them how you have been abusing their point system? I dont get how this is much different? You are abusing their system. People were abusing this system (and taking on the risk). That was for them to decide the risk.
You’re right, I do participate in psuedo spending and to me that is not crossing the line. And when the line is crossed, that is why I feel the need to reach out to someone and let them know there’s a bug.
Hilarious justification.
Curious. Why isn’t MS cash-equivalents not crossing the line? Because “everyone” does it? All CC have rules against it in their T&Cs.
Frankly, if you play this game and worry about ethics, you won’t be doing very much. But I can say the same things about the CC companies using deceptive advertising, unpublished rules, canceling accounts and confiscating points. And let’s not get started about their outrageous interest charges.
As for appointing yourself the morality/ethics police and reporting loopholes, you think way too highly of yourself. If companies were paying attention they’d never have to worry about loopholes.
My interpretation of that is the cards are posting as a purchase and that is fine to me. I forget which card’s T&C I was reading, but it had something about cash equivalent purchases weren’t eligible for the sign up bonus spend. Part of my day job is to find bugs and it’s tough to break character and not let someone know
After these bugs are fixed, would you mind doing a postmortem post with more details? thanks!
(would love to see the line of thought, not to exploit current bugs)